Operation Protective Edge: A Historical Overview
Today, we take a journey back to a pivotal moment in Jewish history: Operation Protective Edge, which commenced on July 8, 2014.
https://www.instagram.com/p/CCY6NoNl9G-/
Understanding the Precursors to Operation Protective Edge
Operation Protective Edge, or Tzuk Eitan in Hebrew, marked a fifty-day Israeli operation in response to the rocket barrages fired from the Gaza Strip by Hamas. This followed the abduction and murder of three Israeli teenagers by Hamas in June 2014.
The Inception and Stages of the Operation
Between June 12 and July 7, approximately 300 rockets were launched from Gaza towards southern Israeli towns, triggering Operation Protective Edge with the aim to safeguard Israeli citizens. The operation had various stages, starting with the targeted air raids on weapon storage facilities and Hamas leadership between July 8-17. Despite these efforts, over 1500 rockets were launched by Hamas during this period.
Breaking the Ceasefire
The first short-lived ceasefire was initiated on July 15. However, Hamas rejected this and resumed rocket attacks on Israel. On July 17, Israel launched Stage 2, which involved ground assaults into Gaza to dismantle the tunnels Hamas used for infiltrating Israel.
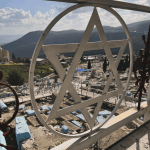
Discovery of Tunnel Entrances and Ceasefire Violations
The Israel Defense Forces (IDF) discovered tunnel entrances in schools, mosques, and civilian homes in Gaza, and exits within Israeli residences and communal buildings. On August 5, Israel agreed to the second Egyptian-mediated ceasefire agreement and withdrew ground forces, but this ceasefire was also violated by Hamas. The final ceasefire was implemented on August 26.
The Aftermath of Operation Protective Edge
During the 50-day conflict, over 4,700 rockets were fired into Israel, with the Iron Dome intercepting around 600 of these. The conflict resulted in thousands of Gazan civilian deaths, over 750 terrorists neutralized, 66 fallen IDF soldiers, six Israeli civilian casualties, and substantial financial damage.
Resources
For more information and context, the following resources were used in compiling this post and provide further reading:
Instagram Post:
https://www.instagram.com/p/CCY6NoNl9G-/
Hashtags:
Judaism, Jewish, History, Jewish History, Israel, Protective Edge, On This Day, Zionism, IDF
Image Source:
17 Captivating Photos from Operation Protective Edge
Text Source:










Start the discussion at community.jewishoriginal.com